Smart Info About How To Detect Hackers

To find a hacker that may be connected to your computer, run tcpview and accept the license agreement.
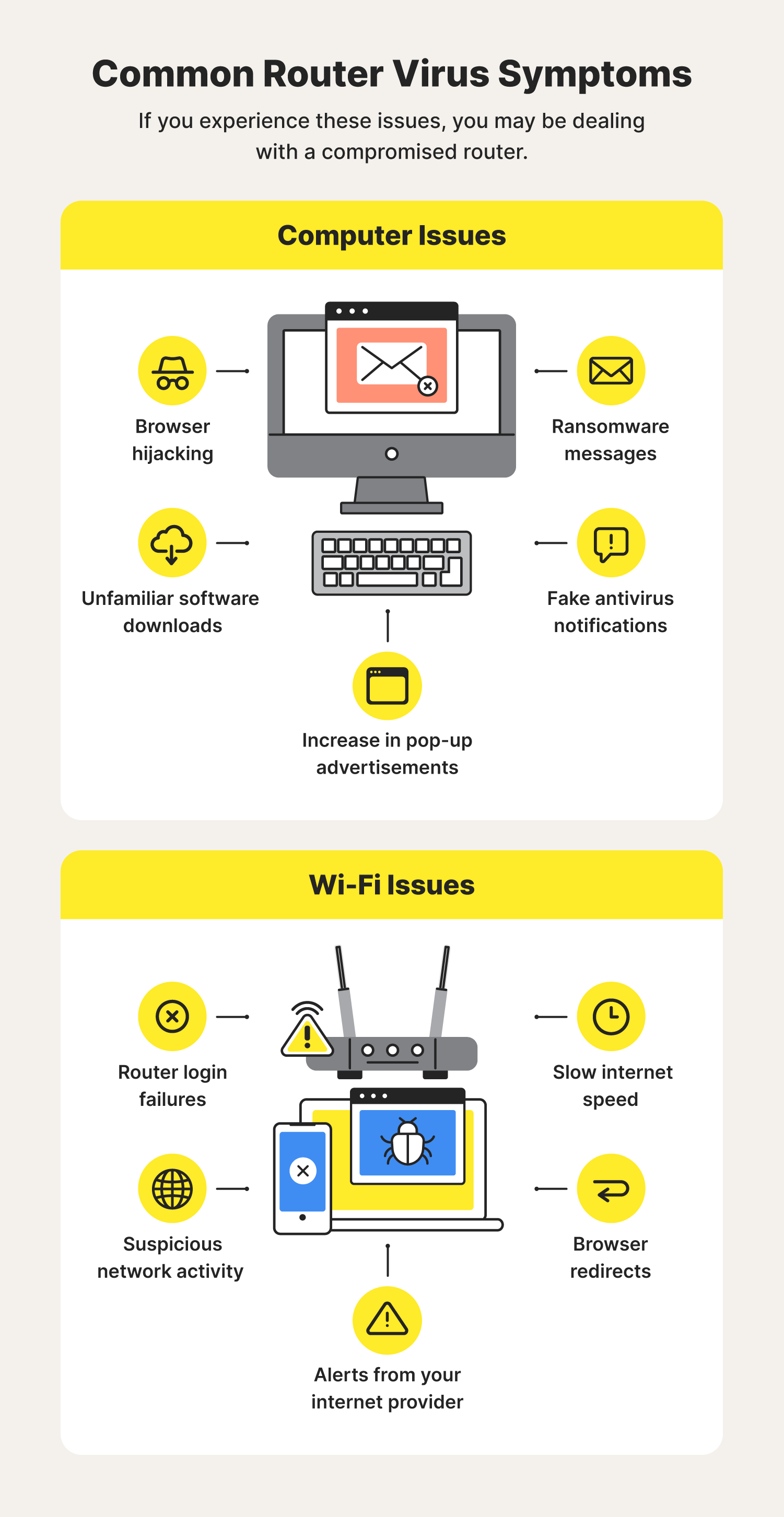
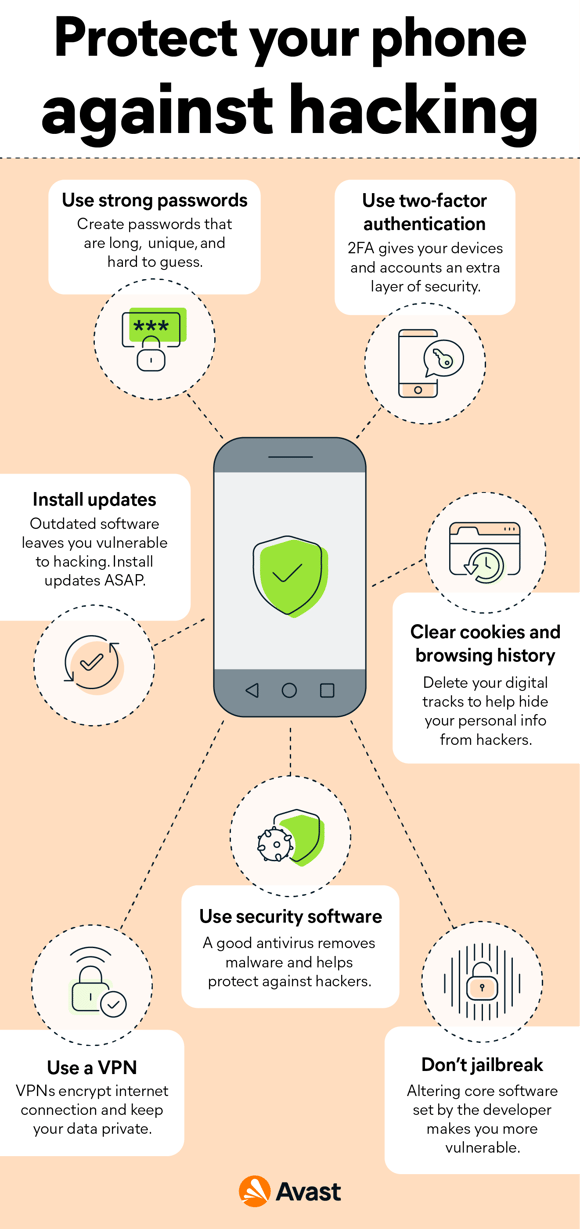
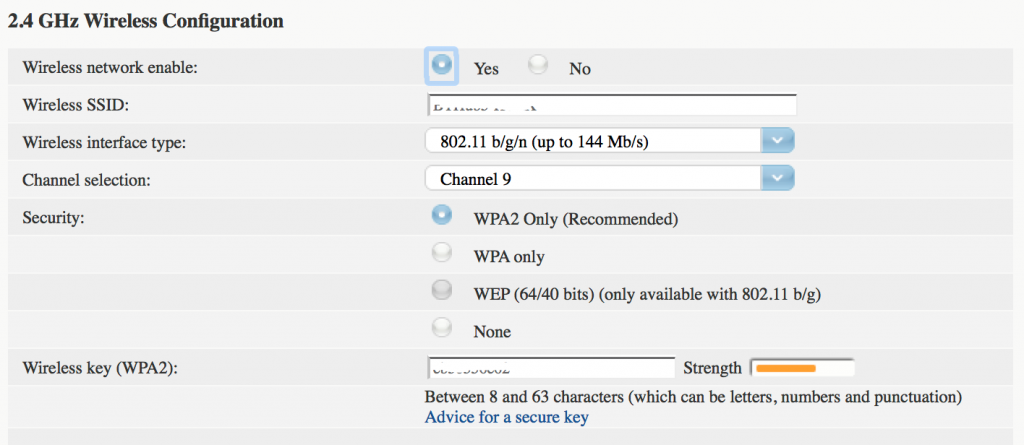
How to detect hackers. This way you can see how many devices are registered on your network and if any of them do not look familiar. This is the most common symptom of a hacked pc but people often blame old devices or bad internet. Multiple layers of protection for cyber security.
How do i detect if a hacker is accessing the computer? You can find a hacker at any moment. First of all check if any rogue programs or services are running.
Watch the player and see if he can walk fast on the water.if you are on 1.8 or higher, there is an enchantment (depth strider) that can do that, so if the player has enchanted. You can use the traceart command to find the hostname of the ip address that the hacker is using to access your machine. How to detect hackers on your network:
Irc clients are another common way for a hacker to get into a computer or remotely control thousands of computers. You will now be shown a page that displays all of the active. Up to 80% cash back 9.
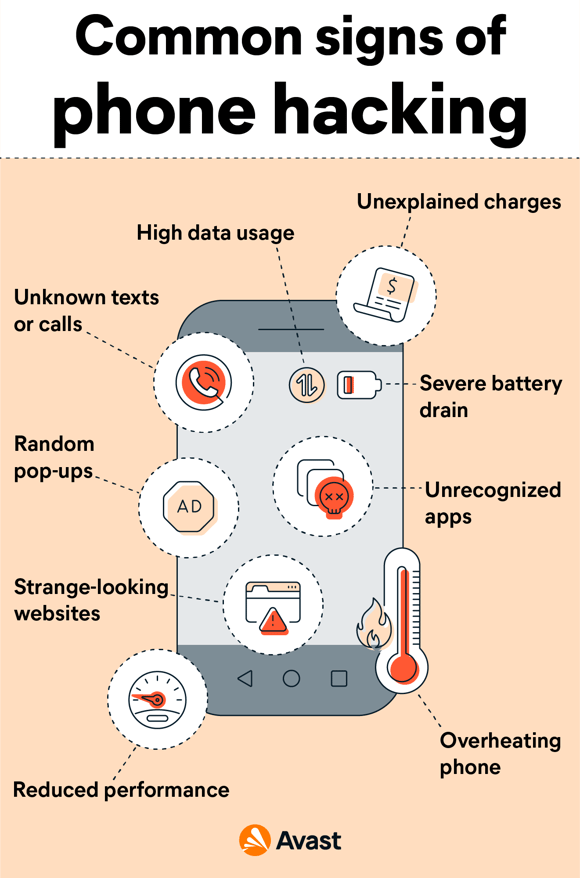
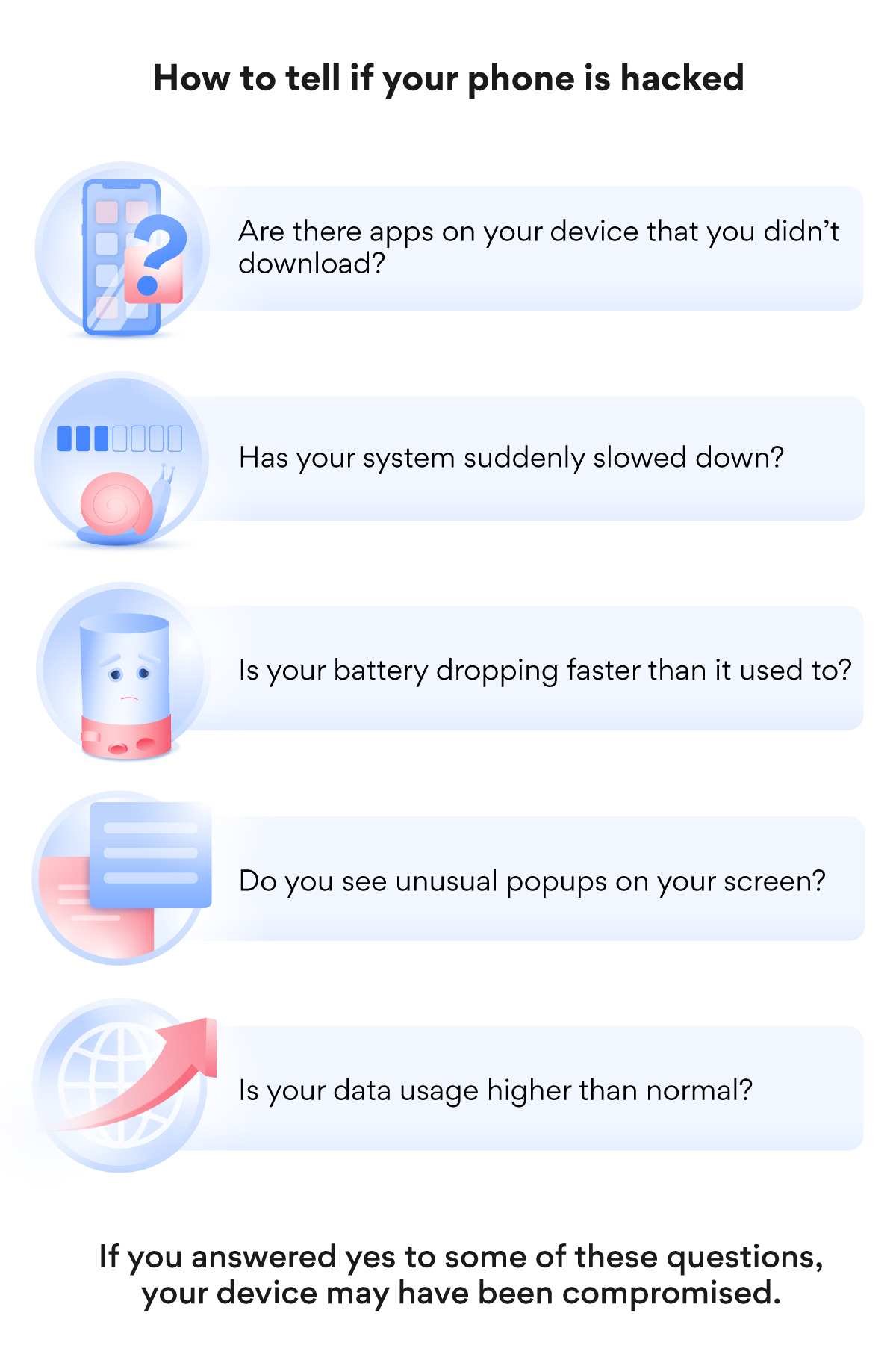
First thing to do after suspicion of a hacker attack is to setup an ids (intrusion detection system) to detect. This video is the updated version of how to check easily if you have been hacked or not, this is not some reliable method, its just a way to check it quickly. If you send or receive some strange text messages automatically, it could be a sign that your phone has been.
This could just mean that there’s a setting you need to change, or it could mean. Open a run window (windows logo key+r), type. Your device is slow and your programs crash.
When accepted procedures exist regarding new software installation, one telltale sign that your. A world of adventure awaits. Certain ip addresses send too many connection requests.
You should start with checking the devices associated with your router. Five command line tools to detect windows hacks. A phone’s battery draining too quickly can be a sign that there’s something going on in the background.
Lateral movement refers to a group of methods cyber criminals use to explore an infected network to find vulnerabilities, escalate access privileges, and reach their ultimate target. In this video on how to know if your computer is hacked?, we will undersatand what is hacking, see some points to identify if our system is hacked or not, th. The first telltale signs of hacking are unusually high k/d or f/d ratio, they do not necessarily mean they are hacking but they should be screened for potential hacking.
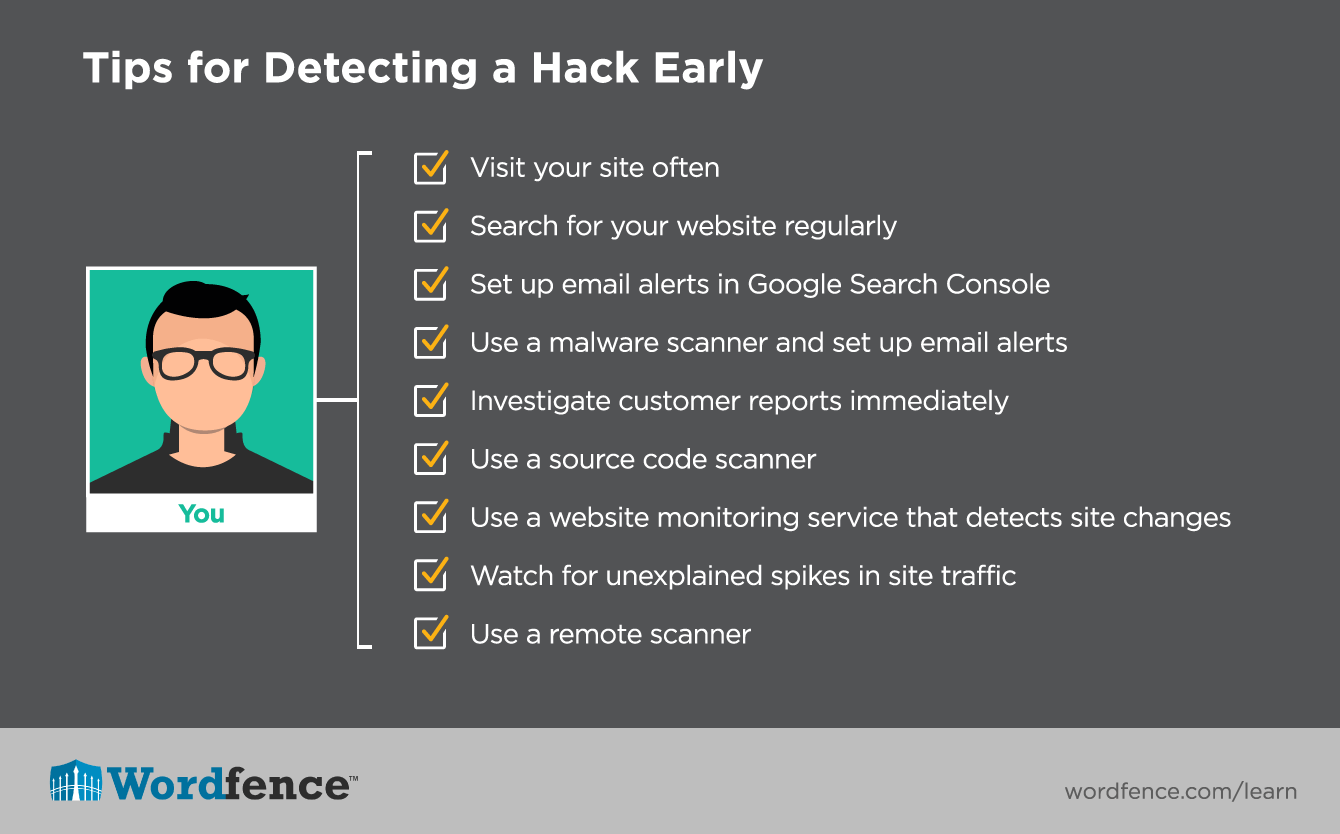
Make sure you are aware of the following red flags to be able to detect a ddos attack before it takes a full swing: Install a intrusion detection system (ids) to know if the system has been hacked. Some tips when catching hackers: